
FTC Safeguards Rule for Auto Dealers
The Federal Trade Commission (FTC) has created additional Frequently Asked Questions (FAQs) to aid auto dealers in adhering to the Gramm-Leach-Bliley Act and the FTC’s Privacy Rule. These FAQs provide clarity on how the Privacy Rule pertains to particular scenarios that auto dealers might face. Let’s delve into some key points:
1. Activities Covered by the Privacy Rule
The Privacy Rule applies to car dealers who:
- Offer credit to an individual (ex. through a retail installment contract) to facilitate the purchase of a car for personal, family, or household use.
- Facilitate financing or leasing for a car intended for personal, family, or household use.
- Deliver financial guidance or counseling to individuals.
If you are involved in any of these activities, any personal information you gather to offer these services falls under the purview of the Privacy Rule. This personal information encompasses details such as an individual’s name, address, phone number, or other identifying information.
Moreover, the Privacy Rule applies even if you collect personal information about someone in the context of potential financing or leasing, even if they do not complete a formal application. However, it does not apply if a person purchases a car with cash or arranges financing independently through another lender.
2. Privacy Notices
If someone expresses interest in buying a car or asks general financing questions, there is no requirement to provide a privacy notice. However, if the person shares personal information related to a potential transaction (such as requesting a quote for a financial package), additional obligations may apply. The timing of providing a privacy notice depends on whether the individual is classified as a “consumer” or a “customer” under the Privacy Rule.
3. Legal Obligations
Please be aware that this information does not cover any potential legal responsibilities you might have under the FTC Safeguards Rule, the Fair Credit Reporting Act, or other federal and state regulations.
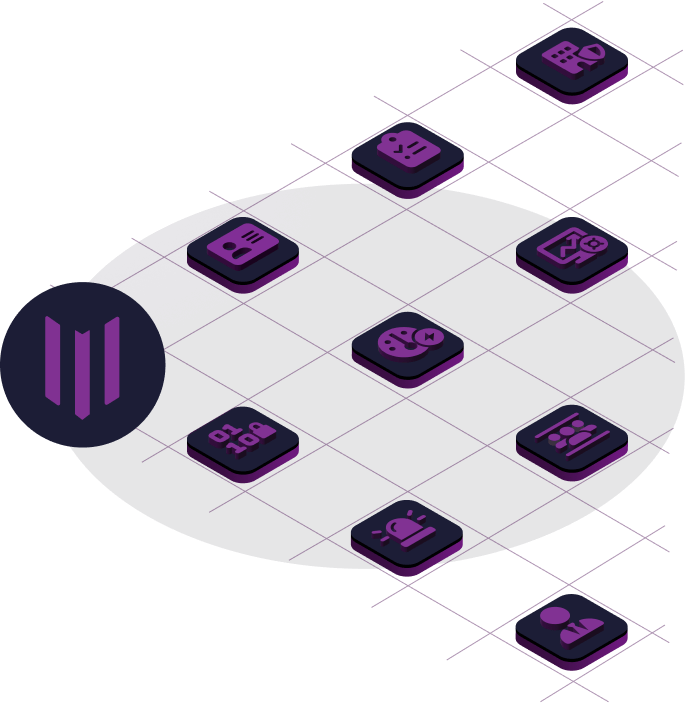
Ensure FTC Safeguards Rule Requirements
To ensure compliance with all nine requirements of the FTC Safeguards Rule, our comprehensive solution provides you with the necessary tools and guidance. From procedural protocols to technical measures and contractual obligations, we’ve got you covered. Safeguarding consumer and personal data is our priority, and our solution empowers you to meet these obligations effectively.
Section 314.4 by the FTC Safeguards Rule.
a. Designate a Qualified Individual
b. Conduct a risk assessment
c. Design and implement safeguards
d. Regularly monitor safeguards
e. Train your staff
f. Monitor your service provider
j. Keep information security program current
h. Create a written incident response plan
k. Report to board of directors

Comply with Benchmark Standards
Evaluate compliance with benchmark standards, such as the CIS Foundations Benchmark for Amazon Web Services, to safeguard your cloud platform.

Safeguard your Cloud Management Plane
The Cloud Security Alliance has consistently identified controls over the cloud management plane as absolutely critical for platform security. Ensure your account is configured appropriately.

Safeguard Corporate Reputation and Data
Let us help maintain your reputation as cybersecurity, legal, or regulatory incidents have increasingly large reputational costs in addition to other penalties.

Avoid Fines for Non-compliance
Evaluate compliance with benchmark standards, such as the CIS Foundations Benchmark for Amazon Web Services, to safeguard your cloud platform.

Safeguard your Cloud Management Plane
The Cloud Security Alliance has consistently identified controls over the cloud management plane as absolutely critical for platform security. Ensure your account is configured appropriately.

Safeguard Corporate Reputation and Data
Let us help maintain your reputation as cybersecurity, legal, or regulatory incidents have increasingly large reputational costs in addition to other penalties.
External Exploitative Penetration Test
In order to clarify any questions you may have. Learn more
Internal Vulnerability Assessment
In order to clarify any questions you may have. Learn more

 Automotive
Automotive Contruction
Contruction Retail
Retail Manufacturing
Manufacturing Shopping
Shopping Healthcare
Healthcare Travel
Travel Technology
Technology Hospitality
Hospitality Insurance
Insurance Transportation
Transportation.svg) Legal
Legal Apps & Software
Apps & Software Real Estate
Real Estate HR
HR